While both Lunar.dev MCPX and TrueFoundry provide foundational connectivity; their architectural philosophies diverge sharply. Strategic decision-makers must distinguish between a platform designed for rapid, UI-driven prototyping and one engineered for high-availability resilience, identity-scoped isolation, and rigorous security governance.
.png)
Both Lunar.dev and TrueFoundry address the "fragmented infrastructure" problem by centralizing MCP connections. Without a gateway, organizations face "credential sprawl" and "IT zero visibility," where API keys are scattered across local developer environments. Centralizing these connections into a unified registry allows enterprises to transition to a governed state where every tool invocation is auditable.
.png)
The primary business outcome of these shared features is the mitigation of Excessive Agency
(OWASP LLM08). By moving from "Before" (unmanaged tool sprawl) to "After" (Unified Registry), administrators can define exactly which tools an agent is eligible to use. This centralized oversight eliminates the risk of agents discovering and exploiting sensitive, unvetted tools that were previously "hidden" in fragmented developer configurations.
Architectural design determines system isolation, throughput, and the granularity of forensic auditing. In high-traffic environments, a failure in a single agent workflow must not compromise the entire ecosystem.
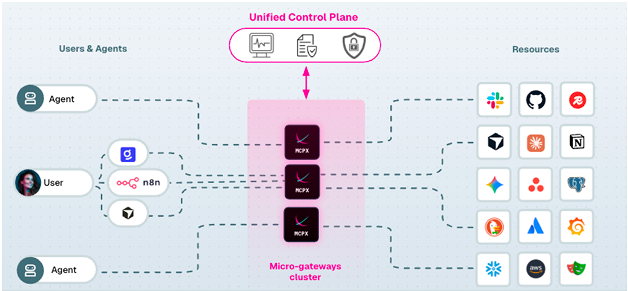
TrueFoundry utilizes a Gateway Plane architecture built on the Hono framework. It functions as a stateless proxy that performs in-memory checks for authentication and rate-limiting, utilizing NATS for real-time configuration syncing from the control plane. This model is optimized for performance, capable of handling 250-350 RPS per pod with minimal overhead.Lunar.dev employs a Microgateway Architecture, deploying a distributed cluster of micro-gateways that enforce identity-scoped access. A critical technical differentiator for Lunar is the ability to deploy these micro-gateways within the organization’s existing VPC or cluster. This ensures data residency and prevents egress of sensitive metadata. In the event of an anomaly or breach, administrators can isolate or block individual agents at the microgateway level without impacting the rest of the cluster.
Lunar.dev is built for the modern telemetry stack, enabling architects to export raw logs and build tailored OpenTelemetry (OTEL) dashboards for deep-tier visibility.
TrueFoundry relies on its internal UI dashboards, backed by a Clickhouse/BlobStorage logging backend. While efficient for high-level monitoring, Lunar’s OTEL-native approach allows for better integration into enterprise-wide SIEM and observability platforms.
Lunar’s architecture collects metrics at the individual Agent Environment level, providing a forensic-level audit trail that surpasses aggregated gateway metrics.
Utilizes a Gateway Plane architecture built on the Hono framework. It functions as a stateless proxy that performs in-memory checks for authentication and rate-limiting, utilizing NATS for real-time configuration syncing from the control plane. This model is optimized for performance, capable of handling 250-350 RPS per pod with minimal overhead.
Employs a Microgateway Architecture, deploying a distributed cluster of micro-gateways that enforce identity-scoped access. A critical technical differentiator for Lunar is the ability to deploy these micro-gateways within the organization’s existing VPC or cluster. This ensures data residency and prevents egress of sensitive metadata. In the event of an anomaly or breach, administrators can isolate or block individual agents at the microgateway level without impacting the rest of the cluster.utilizes a Gateway Plane architecture built on the Hono framework. It functions as a stateless proxy that performs in-memory checks for authentication and rate-limiting, utilizing NATS for real-time configuration syncing from the control plane. This model is optimized for performance, capable of handling 250-350 RPS per pod with minimal overhead.
.png)
In an MCP-enabled environment, the attack surface includes tool poisoning and prompt injection. A security-first mandate is required to operationalize OWASP recommendations through a risk-scoring engine.
.png)
Lunar.dev maps its security features directly to the OWASP Top 10 for LLMs:
MCP Evaluation Sandbox: Admins test server behavior (permissions, token usage) in total isolation before promotion. This provides critical protection against "Rug Pulls" (where a server updates silently to a malicious version) and Version Drift.
Risk-Scoring Engine: Automatically classifies tools into Critical, High, Medium, or Low risk, specifically targeting LLM01 (Prompt Injection) and LLM08 (Excessive Agency).
Secret Management: Structurally, Lunar never stores or manages secrets. It references them from providers like HashiCorp Vault or AWS Secrets Manager and injects them at runtime. Credentials are never exposed to users or configuration files.
Hardening: Admins can "harden" tools by restricting parameters (e.g., limiting a file tool to a specific directory) before releasing secure versions to the registry.
.png)
Lunar.dev maps its security features directly to the OWASP Top 10 for LLMs:
MCP Evaluation Sandbox: Admins test server behavior (permissions, token usage) in total isolation before promotion. This provides critical protection against "Rug Pulls" (where a server updates silently to a malicious version) and Version Drift.
Risk-Scoring Engine: Automatically classifies tools into Critical, High, Medium, or Low risk, specifically targeting LLM01 (Prompt Injection) and LLM08 (Excessive Agency).
Secret Management: Structurally, Lunar never stores or manages secrets. It references them from providers like HashiCorp Vault or AWS Secrets Manager and injects them at runtime. Credentials are never exposed to users or configuration files.
Hardening: Admins can "harden" tools by restricting parameters (e.g., limiting a file tool to a specific directory) before releasing secure versions to the registry.
Lunar.dev utilizes Intent-Based Discovery to solve context management. Using the defer_loading: true flag and a search primitive, the gateway moves from "Static Injection" to "Dynamic Selection":The agent initially sees only a search primitive (~500 tokens).
The agent identifies intent and calls the search tool.The gateway returns 3-5 relevant tool_reference objects (~3,000 tokens).Total context footprint: ~8.7K tokens (vs. 77K).
In an MCP-enabled environment, the attack surface includes tool poisoning and prompt injection. A security-first mandate is required to operationalize OWASP recommendations through a risk-scoring engine.
In the Lunar ecosystem, a Skillset acts as the primary container, holding specific Tool Groups and MCP Prompts. This allows architects to build "Financial Analyst" or "DevOps" skillsets that are shared across agents and teams, ensuring consistent, deterministic behavior.In an MCP-enabled environment, the attack surface includes tool poisoning and prompt injection. A security-first mandate is required to operationalize OWASP recommendations through a risk-scoring engine.
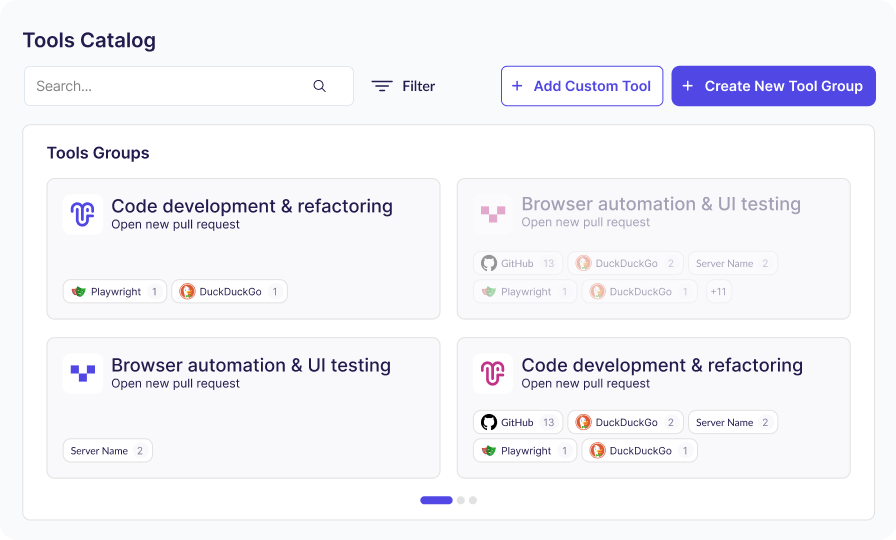
Lunar's tool customization allows organizations to fine-tune and carefully scope the specific tools, parameters, and permissions an AI agent can access, even enabling administrators to instantly toggle specific tool functions (like read versus write access) without modifying any underlying code.
By organizing capabilities into curated "Tool Groups" tailored for specific workflows, this customization significantly improves the agent's decision-making accuracy by eliminating distracting or ambiguous options
TrueFoundry provides Virtual MCP Servers, which allow administrators to combine tools from multiple servers into a curated subset. While effective for basic tool scoping, it currently only supports listing and calling tools.
Lunar.dev extends this capability by supporting MCP Prompts as runtime control surfaces, enabling prompts to encode intent explicitly and guide the agent’s reasoning mode from the start.
The choice between Lunar.dev and TrueFoundry is a choice between a connectivity proxy and a governance infrastructure.
You require a simple, UI-driven playground for rapid prototyping and basic guardrails.ABAC-based policy management is a requirement for a smaller, centralized development team.
You require a high-availability Microgateway Architecture deployed within your VPC/cluster for data residency. Rigorous security is paramount, requiring an MCP Evaluation Sandbox with drift detection and "Rug Pull" protection.
You must optimize context windows and costs through Intent-Based Discovery and defer_loading mechanisms.You require full lifecycle governance of the MCP ecosystem, including secret referencing, tool hardening, and OWASP-aligned risk scoring.
Adopt an enterprise MCP gateway now, then unify governance across LLM and API traffic as usage scales.